There's an expansion in the volume of DDoS, botnet, and malware assaults happening each day. In this time, actualizing a powerful digital danger insight system for gathering, merging, and breaking down the entirety of your log information and danger knowledge takes care of in one spot is a shrewd move for information security and the organization's main concern.
SolarWinds Security Event Manager (SEM) is an on-premise, progressed SIEM instrument worked with a functioning danger insight the board framework as danger takes care of intended to consequently identify and react to client, application, and system dangers.
Banner danger occasions with digital danger knowledge systems
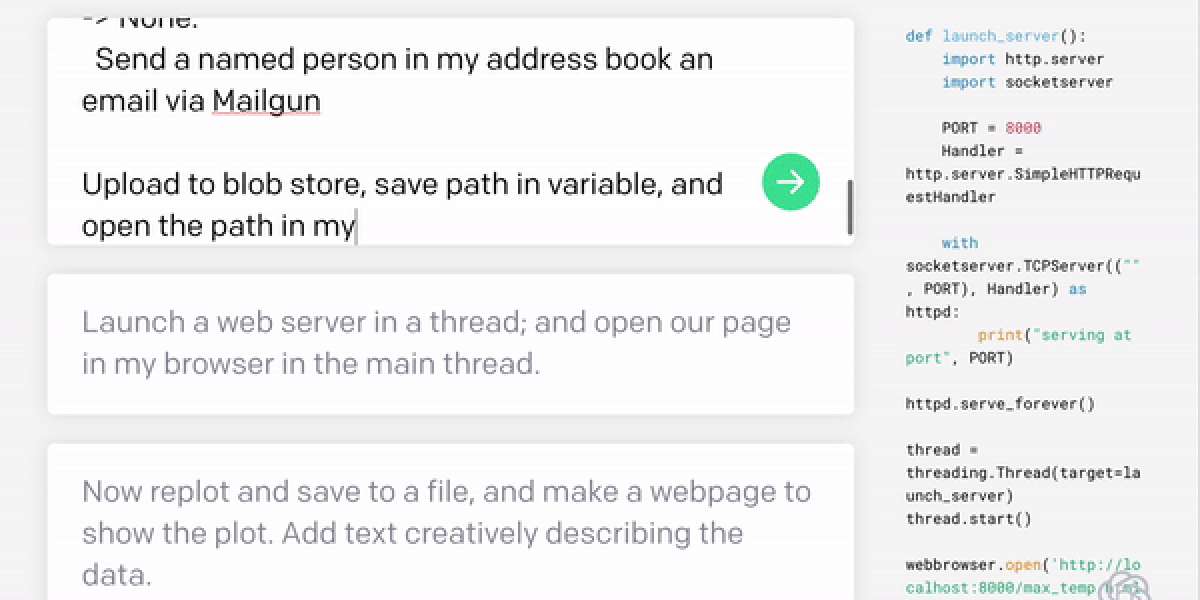
Security Event Manager is worked to gather logs,cybersecurity solutions associate occasions, and screen danger information records, all in a brought together area. The ceaselessly refreshed danger insight feeds can proactively give cyberthreat investigation of exercises against a rundown of known noxious danger vectors, and are intended to quickly alarm you when realized awful on-screen characters have entered your condition or client arranged system security edges have been activated.
Envision that unusual special client movement happens outside of the standard working hours, which can be an indication of vindictive inward conduct. Utilizing its incorporated danger insight, SEM is worked to analyze security occasions against danger takes care of that are refreshed every day, and ready when one of the source or goal fields hit a boycott IP address or area to naturally pinpoint potential security issues like phishing endeavors, malware diseases, and outer cyberattacks.
Security Event Manager additionally accompanies more than 700 inherent connection rules and several dynamic reactions that administrators can arrange to consequently trigger to react to security occasions progressively. You can choose from predefined rules or physically characterize rules to set operational limits, effectively computerizing how SEM mitigates quick dangers and creates applicable notices in light of characterized conditions.
You can all the more effectively recognize inclines inside a lot of danger information by utilizing the inherent perception and disclosure strategies in SEM, including defined pursuit, tree maps, graphs, and word mists. These highlights help in sifting through the characteristic clamor present in log information and can permit you to all the more rapidly recognize significant cyberthreat security occasions, as dubious conduct and information peculiarities. You can spare these scans for sometime in the future and even fare them as reports in PDF or CSV design. SEM additionally offers a broad library of reports, which can be utilized out-of-the container or modified for consistence and criminological investigation.